Hybrid (All compulsory parts can be completed remotely. Some optional parts are only carried out physically.)
EP279V Cyber Security Analysis 3.0 credits
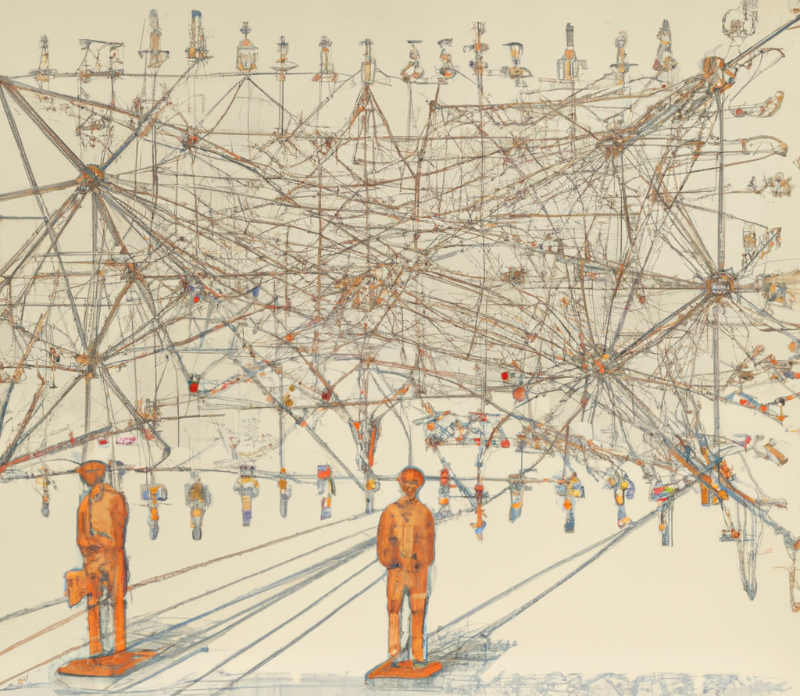
Become more secure with cyber security knowledge. In this course, you will learn methods to analyse threats, risks and defence of large systems against cyber attacks. It will streamline your security work and improve your organisation's protection.
Information per course offering
Information for Autumn 2026 Start 26 Oct 2026 single courses students
- Course location
KTH Campus
- Duration
- 26 Oct 2026 - 11 Jan 2027
- Periods
Autumn 2026: P2 (3 hp)
- Pace of study
17%
- Application code
11840
- Form of study
Distance Daytime
- Language of instruction
English
- Course memo
- Course memo is not published
- Number of places
10 - 15
- Target group
- Professionals in cybersecurity alternatively with interest to learn the basics of cybersecurity.
- Planned modular schedule
- [object Object]
- Schedule
- Schedule is not published
- Part of programme
- No information inserted
Please note that Students not located in Sweden may have problems attending a course at KTH.
You could meet obstacles if you're required to pay fees or if you do not have a Swedish Mobile BankID.
Contact
Course syllabus as PDF
Please note: all information from the Course syllabus is available on this page in an accessible format.
Course syllabus EP279V (Spring 2026–)Content and learning outcomes
Course disposition
Course contents
This course teaches a threat modeling-based method for analyzing cybersecurity risks for systems-of-systems. It includes developing and combining models for computer system resilience, threat actor capabilities, and business impacts of realized threats into an overall cyber risk assessment. Moreover the course addresses how cyber risk analysis is used for identifying and arguing for cost efficient defense mechanism selection for protecting the analyzed system-of-systems.
Intended learning outcomes
After passing the course, the student should be able to
- model threats in large-scale computer systems (including software, networks, etc.)
- describe and evaluate threats and attacks in large-scale computer systems
- describe defence mechanisms for computer system and how they relate to vulnerabilities and attacks
- carry out risk analysis based on a model
- report and present models, a cybersecurity risk analysis, and defense strategies for a computer system
in order to
- understand and explain which threats a specific system can have
- understand and explain how attacks work and propagate through a system architecture
- argue why certain risks should be prioritised
- choose an effective defense to decrease risk.
Literature and preparations
Specific prerequisites
Knowledge and skills in basic programming, 5 credits.
At least one of the following three:
- Knowledge and skills in ethical hacking, 3.5 credits, equivalent to completed course EP274V.
- Knowledge in IT security, 6 credits, equivalent to completed course in cybersecurity, data security, information security, network security or similar.
- At least 3 years of professional experience in a technical role in one of the following areas:
system development, system administration, system architecture, IT architecture, IT security.
English skills equivalent to the upper secondary school course English B/English 6.
Recommended prerequisites
General knowledge in computer science and IT as well as basic experience of working with cyber security.
Literature
Examination and completion
Grading scale
Examination
- PRO1 - Project assignment, 3.0 credits, grading scale: P, F
Based on recommendation from KTH’s coordinator for disabilities, the examiner will decide how to adapt an examination for students with documented disability.
The examiner may apply another examination format when re-examining individual students.
If the course is discontinued, students may request to be examined during the following two academic years.
Examiner
Ethical approach
- All members of a group are responsible for the group's work.
- In any assessment, every student shall honestly disclose any help received and sources used.
- In an oral assessment, every student shall be able to present and answer questions about the entire assignment and solution.
Further information
Course room in Canvas
Offered by
Main field of study
Education cycle
Supplementary information
This course overlaps with EP2790.